PAGE_FAULT_IN_NONPAGED_AREA (50)
Invalid system memory was referenced. This cannot be protected by try-except,
it must be protected by a Probe. Typically the address is just plain bad or it
is pointing at freed memory.
Arguments:
Arg1: fffff88403e31b98, memory referenced.
Arg2: 0000000000000000, value 0 = read operation, 1 = write operation.
Arg3: fffff880040416ec, If non-zero, the instruction address which referenced the bad memory
address.
Arg4: 0000000000000005, (reserved)
Debugging Details:
------------------
Could not read faulting driver name
READ_ADDRESS: GetPointerFromAddress: unable to read from fffff800034b4100
fffff88403e31b98
FAULTING_IP:
ctaud2k+3e6ec
fffff880`040416ec 8b16 mov edx,dword ptr [rsi]
MM_INTERNAL_CODE: 5
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
BUGCHECK_STR: 0x50
PROCESS_NAME: UT2004.exe
CURRENT_IRQL: 0
TRAP_FRAME: fffff88009756270 -- (.trap 0xfffff88009756270)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=fffff880040552e0 rbx=0000000000000000 rcx=fffffa8007b3d010
rdx=000000000000000e rsi=0000000000000000 rdi=0000000000000000
rip=fffff880040416ec rsp=fffff88009756400 rbp=fffff88009756440
r8=fffff88009756441 r9=000000000000003f r10=fffff880040552e0
r11=fffff88004051380 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz na pe nc
ctaud2k+0x3e6ec:
fffff880`040416ec 8b16 mov edx,dword ptr [rsi] ds:65f0:00000000`00000000=????????
Resetting default scope
LAST_CONTROL_TRANSFER: from fffff8000322f3cf to fffff80003284d00
STACK_TEXT:
fffff880`09756108 fffff800`0322f3cf : 00000000`00000050 fffff884`03e31b98 00000000`00000000 fffff880`09756270 : nt!KeBugCheckEx
fffff880`09756110 fffff800`03282e2e : 00000000`00000000 fffff884`03e31b98 fffffa80`0770a100 fffffa80`03d86008 : nt! ?? ::FNODOBFM::`string'+0x44891
fffff880`09756270 fffff880`040416ec : 00000101`80000001 fffff880`09756460 00000000`0000000e fffff880`04042425 : nt!KiPageFault+0x16e
fffff880`09756400 00000101`80000001 : fffff880`09756460 00000000`0000000e fffff880`04042425 fffffa80`07b3d010 : ctaud2k+0x3e6ec
fffff880`09756408 fffff880`09756460 : 00000000`0000000e fffff880`04042425 fffffa80`07b3d010 fffff880`0403b1b0 : 0x101`80000001
fffff880`09756410 00000000`0000000e : fffff880`04042425 fffffa80`07b3d010 fffff880`0403b1b0 00000000`00000000 : 0xfffff880`09756460
fffff880`09756418 fffff880`04042425 : fffffa80`07b3d010 fffff880`0403b1b0 00000000`00000000 00000000`00800000 : 0xe
fffff880`09756420 fffffa80`07b3d010 : fffff880`0403b1b0 00000000`00000000 00000000`00800000 fffffa80`00000100 : ctaud2k+0x3f425
fffff880`09756428 fffff880`0403b1b0 : 00000000`00000000 00000000`00800000 fffffa80`00000100 fffffa80`03d86110 : 0xfffffa80`07b3d010
fffff880`09756430 00000000`00000000 : 00000000`00800000 fffffa80`00000100 fffffa80`03d86110 3ff00000`00000010 : ctaud2k+0x381b0
STACK_COMMAND: kb
FOLLOWUP_IP:
ctaud2k+3e6ec
fffff880`040416ec 8b16 mov edx,dword ptr [rsi]
SYMBOL_STACK_INDEX: 3
SYMBOL_NAME: ctaud2k+3e6ec
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: ctaud2k
IMAGE_NAME: ctaud2k.sys
DEBUG_FLR_IMAGE_TIMESTAMP: 4ba21a22
FAILURE_BUCKET_ID: X64_0x50_ctaud2k+3e6ec
BUCKET_ID: X64_0x50_ctaud2k+3e6ec
Followup: MachineOwner
---------
0: kd> lmvm ctaud2k
start end module name
fffff880`04003000 fffff880`040d4d80 ctaud2k T (no symbols)
Loaded symbol image file: ctaud2k.sys
Image path: \SystemRoot\system32\drivers\ctaud2k.sys
Image name: ctaud2k.sys
Timestamp: Thu Mar 18 13:18:42 2010 (4BA21A22)
CheckSum: 000D3E03
ImageSize: 000D1D80
Translations: 0000.04b0 0000.04e4 0409.04b0 0409.04e4
Self Build DIY OS
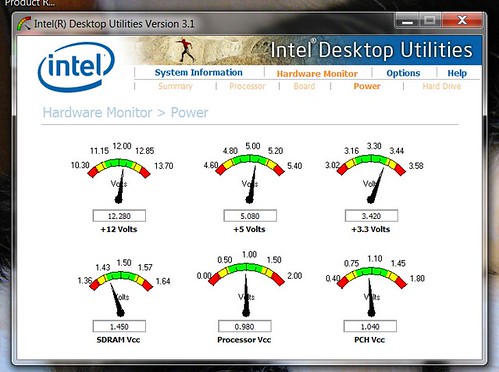
Windows 7 Pro 64bit OEM CPU
Intel i3 Motherboard
Intel DQ67SW Memory
4 Gig DDR3 Graphics Card(s)
GeForce GT 430 Sound Card
Sound Blaster Audigy2 zs Monitor(s) Displays
SyncMaster 213t Screen Resolution
N/A Hard Drives
500 gb 7200 rpm PSU
Cooler Master GX 750W Case
Cooler Master Cooling
Fan Keyboard
Microsoft Sidewinder x6 Mouse
Logitec MX518 Internet Speed
Cable Other Info
IGesture touch pad


 Quote
Quote