Krembo welcome to SevenForums
.....
Hi, and thank you for your answer.
I canceled the ESET's firewall , the Windows Firewall was already on.
I've noticed that the same IPs which were shown in those cache poisoning attack messages are the same ones shown under the DNS IPv4 tab inside the network connection status. I cant really tell what is it called in English because my whole system is in Hebrew, I saw that by click on the network small icon on the dashboard, then right click on the network im connected with, ->Status, then ->Details.., and then under the DNS Server of IPv4..
The scan seems to find nothing, except for those PPR weird windows files. all the other are just files meant to crack apps such as keygens , cracks etc.
-------------------------------------------------------------------------
Log:
Malwarebytes Anti-Malware 1.75.0.1300
Malwarebytes : Free anti-malware download
Database version: v2013.07.07.02
Windows 7 Service Pack 1 x64 NTFS
Internet Explorer 10.0.9200.16618
user :: USER-PC [administrator]
07/07/2013 14:53:10
mbam-log-2013-07-07 (14-53-10).txt
Scan type: Full scan (C:\|G:\|J:\|)
Scan options enabled: Memory | Startup | Registry | File System | Heuristics/Extra | Heuristics/Shuriken | PUP | PUM
Scan options disabled: P2P
Objects scanned: 645388
Time elapsed: 1 hour(s), 29 minute(s), 6 second(s)
Memory Processes Detected: 0
(No malicious items detected)
Memory Modules Detected: 0
(No malicious items detected)
Registry Keys Detected: 1
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\IEXPLORE.EXE (Backdoor.PoisonIvy) -> Quarantined and deleted successfully.
Registry Values Detected: 0
(No malicious items detected)
Registry Data Items Detected: 0
(No malicious items detected)
Folders Detected: 2
C:\Windows\SysWOW64\28463 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\System32\28463 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
Files Detected: 39
C:\Users\user\Downloads\I_D_M_6.12.25.rar (PUP.Hacktool.Patcher) -> No action taken.
G:\Square Enix\Sleeping Dogs\buddha.dll (Malware.Gen.SKR) -> No action taken.
G:\osx\OS X Mountain Lion 10.8.2 VMware Image\VMware Unlocker - Hardware Virtualization Bypasser\vmware-vmx-patch.exe (RiskWare.Tool.CK) -> No action taken.
J:\תוכנות\Internet Download Manager\IDM 6.12.25\I_D_M_6.12.25.rar (PUP.Hacktool.Patcher) -> No action taken.
J:\תוכנות\Internet Download Manager\IDM 6.12.25\Patch\internet.download.manager.v6.08-patch.exe (PUP.Hacktool.Patcher) -> No action taken.
J:\תוכנות\Internet Download Manager\IDM 6.12.25\Patch\internet.download.manager.v6.08-patch.rar (PUP.Hacktool.Patcher) -> No action taken.
J:\תוכנות\Internet Download Manager\Internet Download Manager 6.05B8 by sexh\IDM B8 and crack - by sexh.rar (Trojan.Ardamax) -> No action taken.
J:\תוכנות\VMware.Workstation.v9.0.0.812388.Incl.Keymaker-ZWT\keygen.exe (Riskware.Tool.CK) -> No action taken.
C:\Program Files (x86)\Internet Download Manager\internet.download.manager.v6.08-patch.exe (PUP.Hacktool.Patcher) -> Quarantined and deleted successfully.
C:\Program Files (x86)\Sony\Vegas Pro 11.0\keygen DI v2.0\Keygen.exe (RiskWare.Tool.HCK) -> Quarantined and deleted successfully.
C:\Users\user\Documents\RemoveWAT20\RemoveWAT.exe (HackTool.Wpakill) -> Quarantined and deleted successfully.
C:\Users\user\Documents\RemoveWAT20\RemoveWAT20\R-WAT.txt (HackTool.Wpakill) -> Quarantined and deleted successfully.
C:\Users\user\Documents\RemoveWAT20\RemoveWAT20\RemoveWAT.exe (HackTool.Wpakill) -> Quarantined and deleted successfully.
C:\Users\user\Downloads\ESET PureFix v2.02.rar (RiskWare.Tool.CK) -> Quarantined and deleted successfully.
C:\Users\user\Downloads\IDM B8 and crack - by sexh.rar (Trojan.Ardamax) -> Quarantined and deleted successfully.
C:\Users\user\Downloads\Vegas_Pro_2011.rar.crdownload (RiskWare.Tool.CK) -> Quarantined and deleted successfully.
C:\Users\user\Downloads\eset_nod32-5.rar (RiskWare.Tool.CK) -> Quarantined and deleted successfully.
C:\Users\user\Downloads\keygen.DI.v2.0..rar (RiskWare.Tool.HCK) -> Quarantined and deleted successfully.
C:\Users\user\Downloads\rpc412_setup.exe (PAssword.Tool) -> Quarantined and deleted successfully.
C:\Users\user\Downloads\הפריצה רשמית ולכל החיים בגירסא חדשה לנוד32 גירסא 5.rar (RiskWare.Tool.CK) -> Quarantined and deleted successfully.
C:\Windows\SysWOW64\28463\PRTT.001 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\SysWOW64\28463\PRTT.002 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\SysWOW64\28463\PRTT.005 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\SysWOW64\28463\PRTT.006 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\SysWOW64\28463\PRTT.007 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\System32\28463\PRTT.001 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\System32\28463\PRTT.002 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\System32\28463\PRTT.005 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\System32\28463\PRTT.006 (PUP.ArdamaxKeyLogger) -> Quarantined and deleted successfully.
C:\Windows\System32\28463\PRTT.006 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\System32\28463\PRTT.007 (Keylogger.Ardamax) -> Quarantined and deleted successfully.
C:\Windows\System32\28463\PRTT.007 (PUP.ArdamaxKeyLogger) -> Quarantined and deleted successfully.
G:\Documents\RemoveWAT20\RemoveWAT20\R-WAT.txt (HackTool.Wpakill) -> Quarantined and deleted successfully.
G:\Documents\RemoveWAT20\RemoveWAT20\RemoveWAT.exe (HackTool.Wpakill) -> Quarantined and deleted successfully.
G:\backup\Documents\RemoveWAT20\RemoveWAT20\R-WAT.txt (HackTool.Wpakill) -> Quarantined and deleted successfully.
G:\backup\Documents\RemoveWAT20\RemoveWAT20\RemoveWAT.exe (HackTool.Wpakill) -> Quarantined and deleted successfully.
J:\Portable תקין\Device Doctor 1.0\Data\Native\STUBEXE\@PROGRAMFILES@\Internet Explorer\iexplore.exe (Backdoor.PoisonIvy) -> Quarantined and deleted successfully.
J:\Portable תקין\Device Doctor 1.0\Data\Virtual\STUBEXE\@PROGRAMFILES@\Device Doctor\1.0.0.1\DeviceDoctor.exe (Backdoor.PoisonIvy) -> Quarantined and deleted successfully.
J:\System Volume Information\_restore{E942257D-7E83-485C-886F-EF5B12C3FA67}\RP103\A0023471.exe (Backdoor.PoisonIvy) -> Quarantined and deleted successfully.
(end)
---------------------------------------------------------


 Quote
Quote To enable Windows 7 Firewall
To enable Windows 7 Firewall  Malwarebytes
Malwarebytes 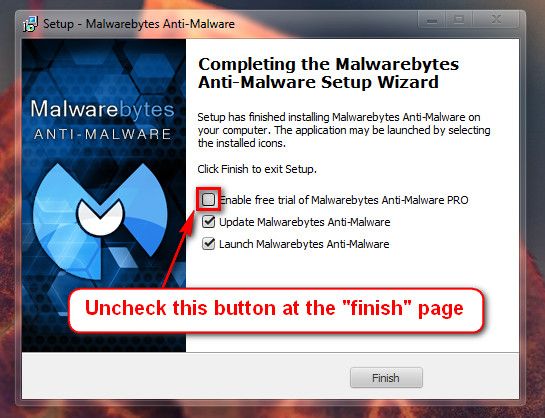
 32-bit Version OS
32-bit Version OS 
 FRST.txt and Addition.txt will be on the Desktop
FRST.txt and Addition.txt will be on the Desktop 
 Keygens, cracks and serials violate copyright and ownership of software. They are used to get programs for free that one should pay for. It is known as software piracy, which is equivalent to stealing. It is essentially the same as if one figured out a way to break into the neighbor's auto and take it.
Keygens, cracks and serials violate copyright and ownership of software. They are used to get programs for free that one should pay for. It is known as software piracy, which is equivalent to stealing. It is essentially the same as if one figured out a way to break into the neighbor's auto and take it.
