New
#11
why do my Restore Points keep disappearing?
-
-
New #12
This all looks so wrong
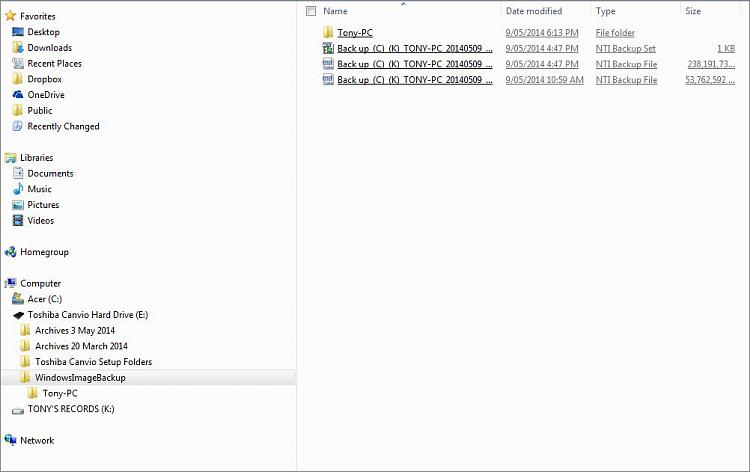
...this is how things look after the NTI Backup...and somehow, it all looks so wrong!
Somehow, my Tony-PC Folder has ended up on the Toshiba External Hard Drive. If I work as the Administrator, can I place it back where it should be? And on that point, I've forgotten where .....advice please to correct.. Note: I have resisted all temptation to eject the Toshiba HD at this stage. What a mess!!
.....advice please to correct.. Note: I have resisted all temptation to eject the Toshiba HD at this stage. What a mess!!

-
New #13
Tony,
Your user folder did not get moved. That's just part of the system image backup. From the blue note box at the top of the tutorial. If you like, you can safely delete the E:\WindowsImageBackup folder to delete the failed system image to recover the hard drive space.
drive letter:\WindowsImageBackup\computer name\Backup YYYY-MM-DD HHMMSS
If you like NTI Backup, then you could use that instead. Macrium Reflect Free is another good program.
-
New #14
2 x Backups failed - Recommended CHKDSK/R run
Thanks for the help Shawn,
OK ... the following two different backup attempts describe the problems clearly.
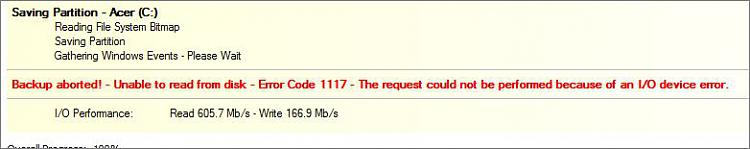

So, in elevated command I ran CHKDSK/R, and then sat back and watched the grass grow. I'm guessing that CHKDSK/R must have scanned the system completely about five [x 5] times over in all, and eventually cleaned out some sectors of 'BAD' files*, before it finally finished after about 8 hours, and rebooted my Laptop.
All restarted better than it has in days, and there is none of the previously noted instability happening now. However, I will continue to monitor the situation for the time being.
I'm presuming that I should be able to access a log of the CHKDSK/R event, but have been unable to locate it. Advice please.
Cheers, Tony
* not the word used to describe the 'bundles', but I've forgotten the correct name
-
New #15
That's great news so far Tony.
See if this may be able to help with the chkdsk log. :)
Check Disk (chkdsk) - Read Event Viewer Log
-
New #16
I am logged in as the Administrator, however, at Windows Log > Application, in the Context Menu - 'Find' is greyed out...
-
-
New #18
Everything I read about your issues sound like malware to me. There are some malware that attempts to hide itself by using restore points. The sneakiest ones remove themselves when you are scanning and throw themselves into a restore point, scheduling it to run as boot. So then when the system restarts the threat is restored. It then deletes the rest of the restore points, so that you cannot do one when it decides to trash your system and undo what it did.
**Let's disable system protection on all drives right now, as this will remove all restore points. Even the latest one that typically cannot be removed. Keep it disabled while we look at your machine. This way the malware (if it exists) has no where to go.** <------Please confirm and tell me you have done this step.
I know you have stated that you have ran all kinds of malware scans, but lets give this one a go...
1.) Download herdprotect: (choose the portable version)
Download herdProtect - Free Anti-Malware Platform
2.) Run the scan.
3.) When the scan finishes, save the results per the screenshot below. Then upload the log here.
DO NOT REMOVE ANYTHING YET. I will advise if anything needs removed when I receive the log.
Attached Images
-
-
New #20
....per advice and instructions. Note: As yet I've not gone near the " ? " for settingsandrew129260;
**Let's disable system protection on all drives right now, as this will remove all restore points. Even the latest one that typically cannot be removed. Keep it disabled while we look at your machine. This way the malware (if it exists) has no where to go.** <------[B said:
Related Discussions

 as you can see.
as you can see.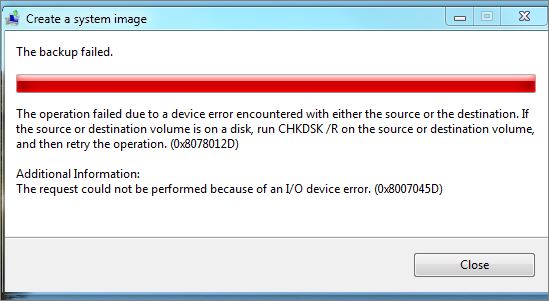

 Quote
Quote