New
#11
These were caused by memory corruption but
WERE NOT VERIFIER ENABLED.
I would run memtest
Download a copy of Memtest86 and burn the ISO to a CD using Iso Recorder or another ISO burning program. Boot from the CD, and leave it running for at least 5 or 6 passes.
Just remember, any time Memtest reports errors, it can be either bad RAM or a bad motherboard slot. Test the sticks individually, and if you find a good one, test it in all slots.
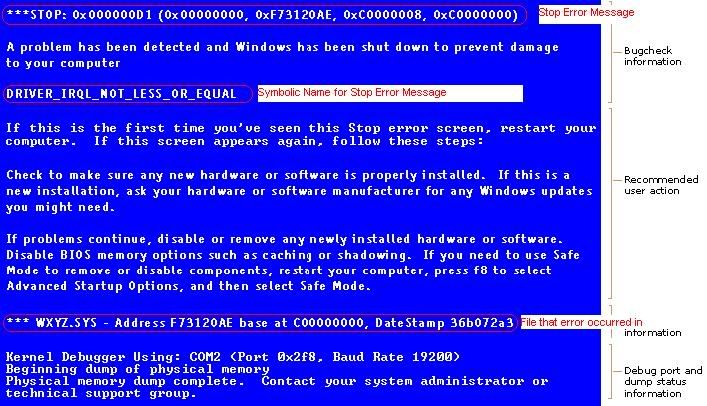
Old driversCode:Microsoft (R) Windows Debugger Version 6.11.0001.404 X86 Copyright (c) Microsoft Corporation. All rights reserved. Loading Dump File [C:\Users\K\Desktop\bsod ver\Windows_NT6_BSOD_jcgriff2\102010-40529-01.dmp] Mini Kernel Dump File: Only registers and stack trace are available Symbol search path is: SRV*C:\Symbols*http://msdl.microsoft.com/download/symbols;srv*e:\symbols *http://msdl.microsoft.com/download/symbols Executable search path is: Windows 7 Kernel Version 7600 MP (8 procs) Free x64 Product: WinNt, suite: TerminalServer SingleUserTS Built by: 7600.16617.amd64fre.win7_gdr.100618-1621 Machine Name: Kernel base = 0xfffff800`02e58000 PsLoadedModuleList = 0xfffff800`03095e50 Debug session time: Wed Oct 20 16:48:30.745 2010 (GMT-4) System Uptime: 0 days 15:20:43.807 Loading Kernel Symbols . Press ctrl-c (cdb, kd, ntsd) or ctrl-break (windbg) to abort symbol loads that take too long. Run !sym noisy before .reload to track down problems loading symbols. .............................................................. ................................................................ .............................................. Loading User Symbols Loading unloaded module list ................... ******************************************************************************* * * * Bugcheck Analysis * * * ******************************************************************************* Use !analyze -v to get detailed debugging information. BugCheck D1, {558, 2, 0, fffff88004201120} *** WARNING: Unable to verify timestamp for win32k.sys *** ERROR: Module load completed but symbols could not be loaded for win32k.sys Probably caused by : memory_corruption Followup: memory_corruption --------- 0: kd> !analyze -v ******************************************************************************* * * * Bugcheck Analysis * * * ******************************************************************************* DRIVER_IRQL_NOT_LESS_OR_EQUAL (d1) An attempt was made to access a pageable (or completely invalid) address at an interrupt request level (IRQL) that is too high. This is usually caused by drivers using improper addresses. If kernel debugger is available get stack backtrace. Arguments: Arg1: 0000000000000558, memory referenced Arg2: 0000000000000002, IRQL Arg3: 0000000000000000, value 0 = read operation, 1 = write operation Arg4: fffff88004201120, address which referenced memory Debugging Details: ------------------ READ_ADDRESS: GetPointerFromAddress: unable to read from fffff800031000e0 0000000000000558 CURRENT_IRQL: 2 FAULTING_IP: netbt!RemoteHashTimeout+16a fffff880`04201120 498b6d00 mov rbp,qword ptr [r13] CUSTOMER_CRASH_COUNT: 1 DEFAULT_BUCKET_ID: CODE_CORRUPTION BUGCHECK_STR: 0xD1 PROCESS_NAME: System TRAP_FRAME: fffff80000b9c320 -- (.trap 0xfffff80000b9c320) NOTE: The trap frame does not contain all registers. Some register values may be zeroed or incorrect. rax=0000000000000002 rbx=0000000000000000 rcx=0000000008493730 rdx=0000000000000000 rsi=0000000000000000 rdi=0000000000000000 rip=fffff88004201120 rsp=fffff80000b9c4b0 rbp=0000000000000100 r8=fffffa801092ad00 r9=0000000000000000 r10=fffffa800a247850 r11=0000000000000002 r12=0000000000000000 r13=0000000000000000 r14=0000000000000000 r15=0000000000000000 iopl=0 nv up ei pl nz na po nc netbt!RemoteHashTimeout+0x16a: fffff880`04201120 498b6d00 mov rbp,qword ptr [r13] ds:00000000`00000000=???????????????? Resetting default scope LAST_CONTROL_TRANSFER: from fffff80002ec7ca9 to fffff80002ec8740 STACK_TEXT: fffff800`00b9c1d8 fffff800`02ec7ca9 : 00000000`0000000a 00000000`00000558 00000000`00000002 00000000`00000000 : nt!KeBugCheckEx fffff800`00b9c1e0 fffff800`02ec6920 : 00000000`00000700 00000000`000003e8 fffff800`00b9c398 00000000`ffffffff : nt!KiBugCheckDispatch+0x69 fffff800`00b9c320 fffff880`04201120 : fffffa80`07f0a000 fffff880`04b33a24 fffffa80`10926c68 fffffa80`10926b10 : nt!KiPageFault+0x260 fffff800`00b9c4b0 fffff880`042011f7 : fffffa80`1092adf0 fffff800`00b9c600 fffffa80`1092adf0 fffffa80`1092ad02 : netbt!RemoteHashTimeout+0x16a fffff800`00b9c540 fffff800`02ed429e : fffff800`00b9c618 00000000`00000000 00000000`40ff0088 00000000`00000000 : netbt!TimerExpiry+0x5b fffff800`00b9c570 fffff800`02ed3dd6 : fffffa80`1092aeb0 00000000`003608ff 00000000`00000000 00000000`00000001 : nt!KiProcessTimerDpcTable+0x66 fffff800`00b9c5e0 fffff800`02ed44be : 00000080`9fe0101c fffff800`00b9cc58 00000000`003608ff fffff800`03047268 : nt!KiProcessExpiredTimerList+0xc6 fffff800`00b9cc30 fffff800`02ed3cb7 : 00000015`b7dffac2 00000015`003608ff 00000015`b7dffa08 00000000`000000ff : nt!KiTimerExpiration+0x1be fffff800`00b9ccd0 fffff800`02ed0eea : fffff800`03042e80 fffff800`03050c40 00000000`00000001 fffff880`00000000 : nt!KiRetireDpcList+0x277 fffff800`00b9cd80 00000000`00000000 : fffff800`00b9d000 fffff800`00b97000 fffff800`00b9cd40 00000000`00000000 : nt!KiIdleLoop+0x5a STACK_COMMAND: kb CHKIMG_EXTENSION: !chkimg -lo 50 -db !netbt 3 errors : !netbt (fffff880042010f9-fffff88004201cf1) fffff880042010f0 02 00 8b 93 b0 01 00 00 8b *1d 7a d1 02 00 88 44 ..........z....D ... fffff88004201be0 83 *eb 20 48 89 41 18 4c 89 51 10 48 8b 44 0a 08 .. H.A.L.Q.H.D.. ... fffff88004201cf0 f6 *51 80 7d 0f 1c b8 01 00 00 c0 48 89 b4 24 b0 .Q.}.......H..$. MODULE_NAME: memory_corruption IMAGE_NAME: memory_corruption FOLLOWUP_NAME: memory_corruption DEBUG_FLR_IMAGE_TIMESTAMP: 0 MEMORY_CORRUPTOR: STRIDE FAILURE_BUCKET_ID: X64_MEMORY_CORRUPTION_STRIDE BUCKET_ID: X64_MEMORY_CORRUPTION_STRIDE Followup: memory_corruption ---------
How To Find Drivers:Code:ISODrv64.sys fffff880`01bcb000 fffff880`01be7000 0x0001c000 0x472be92e 11/2/2007 23:21:18 sncduvc.SYS fffff880`07611000 fffff880`07619a80 0x00008a80 0x495894f2 12/29/2008 05:14:26 spldr.sys fffff880`01610000 fffff880`01618000 0x00008000 0x4a0858bb 5/11/2009 12:56:27 ATK64AMD.sys fffff880`05bc6000 fffff880`05bce000 0x00008000 0x4a0a1cb6 5/12/2009 21:04:54 GEARAspiWDM.sys fffff880`05b9e000 fffff880`05bab000 0x0000d000 0x4a1151c0 5/18/2009 08:17:04 amdxata.sys fffff880`01260000 fffff880`0126b000 0x0000b000 0x4a12f2eb 5/19/2009 13:56:59 ASMMAP64.sys fffff880`04885000 fffff880`0488d000 0x00008000 0x4a4c7a36 7/2/2009 05:13:26- - The most common drivers are listed on this page: Driver Reference- search Google for the name of the driver
- compare the Google results with what's installed on your system to figure out which device/program it belongs to
- visit the web site of the manufacturer of the hardware/program to get the latest drivers (DON'T use Windows Update or the Update driver function of Device Manager).
- if there are difficulties in locating them, post back with questions and someone will try and help you locate the appropriate program.
- - Driver manufacturer links are on this page: Drivers and Downloads


 Quote
Quote