Security and Quality Rollup for .NET Framework 3.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, and 4.7.1 updates for Windows 7 SP1 and Server 2008 R2 SP1 (KB 4055532)
Applies to: Microsoft .NET Framework 4.7.1, Microsoft .NET Framework 4.7, Microsoft .NET Framework 4.6.2, Microsoft .NET Framework 4.6.1, Microsoft .NET Framework 4.6, Microsoft .NET Framework 4.5.2, Microsoft .NET Framework 3.5.1
This update has been released as part of the January 2018 Security and Quality Rollup for .NET Framework 3.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, and 4.7.1 for Windows 7 SP1 and Windows Server 2008 R2 SP1.
Important
If you have not been offered this security update, you may be running incompatible antivirus software, and you should contact the software vendor. We are working closely with antivirus software partners to make sure that all customers receive the January Windows security updates as soon as possible. For more information, go to
Important: Windows security updates released January 3, 2018, and antivirus software. Also, see the
"Additional information about this security update" section in this article.
Summary
This security update resolves a security feature bypass vulnerability that exists when Microsoft .NET Framework and .NET Core components do not completely validate certificates. This security update addresses the vulnerability by helping to make sure that .NET Framework and .NET Core components completely validate certificates. To learn more about this vulnerability, see
Microsoft Common Vulnerabilities and Exposures CVE-2018-0786.
Additionally, this security update resolves a denial of service vulnerability that exists when .NET Framework and .NET Core components improperly process XML documents. This update addresses the vulnerability by correcting how .NET Framework and .NET Core component applications handle XML document processing. To learn more about this vulnerability, see
Microsoft Common Vulnerabilities and Exposures CVE-2018-0764.
Important
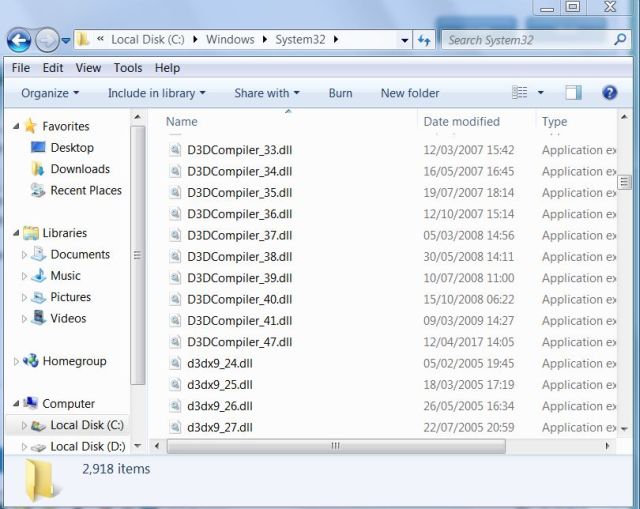
- All updates for .NET Framework 4.6, 4.6.1, 4.6.2, 4.7, and 4.7.1 require that the d3dcompiler_47.dll is installed. We recommend that you install the included d3dcompiler_47.dll before you apply this update. For more information about the d3dcompiler_47.dll, see KB 4019990.
- If you install a language pack after you install this update, you must reinstall this update. Therefore, we recommend that you install any language packs that you need before you install this update. For more information, see Add language packs to Windows.
Additional information about this security update
How to obtain help and support for this security update


 Quote
Quote