New
#1
PUM.Dns re-director found with RogueKiller
I have been finding this on several machines lately using RogueKiller. (Third one today)
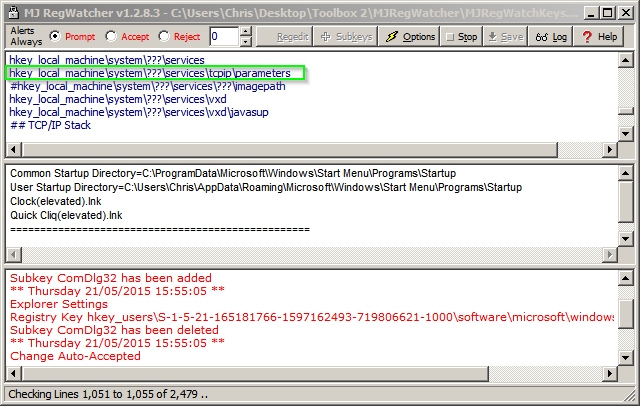
¤¤¤ Registry : 4 ¤¤¤
[PUM.Dns] (X64) HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\Tcpip\Parameters | DhcpNameServer : 10.0.0.1 [(Private Address) (XX)] -> Found
[PUM.Dns] (X64) HKEY_LOCAL_MACHINE\System\ControlSet001\Services\Tcpip\Parameters | DhcpNameServer : 10.0.0.1 [(Private Address) (XX)] -> Found
[PUM.Dns] (X64) HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\Tcpip\Parameters\Interfaces\{B5D00FF2-C635-4597-A707-DEE7ED712F33} | DhcpNameServer : 10.0.0.1 [(Private Address) (XX)] -> Found
[PUM.Dns] (X64) HKEY_LOCAL_MACHINE\System\ControlSet001\Services\Tcpip\Parameters\Interfaces\{B5D00FF2-C635-4597-A707-DEE7ED712F33} | DhcpNameServer : 10.0.0.1 [(Private Address) (XX)] -> Found
The Private address is sometimes different but is always a class A private address.
After rebooting the entries return. Webpages are timing out on multiple browsers and ping returns >50% packet loss.
Suggestions online are to run the standard arsenal: Malewarebytes, AV cleaners, Combofix (Win 7), ESET, ect. None of these are finding the infection.
I have tried all of these and I am still receiving same findings from RogueKiller. It is persistent even when booting to safe mode.
The only solution I have found thus far has been to Refresh the OS.
I am hoping someone finds a less intrusive solution. Any help would be appreciated.


 Quote
Quote