New
#181
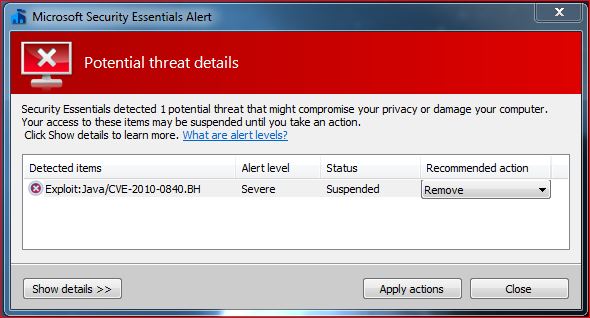
Same here and it is related to MSE according to MS. It can only be tamed by excluding explorer.exe process which is advice from MS.
MSE updated through updates a couple of weeks or more ago. Since then, I'm having a situation with MSE that is troubling me. Once a day, MSE with a random GUI number wants to change registry settings and then load a kernel driver which is fine except for one thing. My HIPS doesn't seem to have the ability to permanently allow the rule because of the daily changing of the random GUI. I could do it by allowing the services process full control but I'm afraid that it would leave me wide open so to speak. Below is the info for such a daily event with the latest MSE. Sorry, it's kinda lengthy but I want the detailed shown in case anyone knows why or a way to overcome the daily ritual of this.
Code:2/3/2011 14:05:45 Set registry value Permitted Process: e:\windows\system32\services.exe Target: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MpKslade2f93a\Start Data: 0x00000004(4) Rule: [Registry Group]Autostarts Locations -> [Registry]HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\*; Start 2/3/2011 14:05:46 Delete registry key Permitted Process: e:\windows\system32\services.exe Target: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MpKslade2f93a Rule: [Registry Group]Autostarts Locations -> [Registry]HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services 2/3/2011 14:05:49 Create registry key Permitted Process: e:\windows\system32\services.exe Target: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MpKsl2df405c0 Rule: [Registry Group]Autostarts Locations -> [Registry]HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services 2/3/2011 14:05:51 Set registry value Permitted Process: e:\windows\system32\services.exe Target: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MpKsl2df405c0\Start Data: 0x00000001(1) Rule: [Registry Group]Autostarts Locations -> [Registry]HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\*; Start 2/3/2011 14:05:52 Set registry value Permitted Process: e:\windows\system32\services.exe Target: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MpKsl2df405c0\ImagePath Data: \??\E:\ProgramData\Microsoft\Microsoft Antimalware\Definition Updates\{6CC745D3-C3D0-4145-8B88-57322F224560}\MpKsl2df405c0.sys Rule: [Registry Group]Autostarts Locations -> [Registry]HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\*; ImagePath 2/3/2011 14:05:56 Load kernel driver Permitted Process: e:\windows\system32\services.exe Target: e:\programdata\microsoft\microsoft antimalware\definition updates\{6cc745d3-c3d0-4145-8b88-57322f224560}\mpksl2df405c0.sys Rule: [App]e:\windows\system32\services.exe


 Quote
Quote