New
#71
Attention: cottonball, virus deleted all SD photos
-
-
New #72
@jumanji,
On target. It is not a good idea to rely on just one result.
@ducat1base,
Hopefully, Yes. :)
 Please run RogueKiller once again, and this time press: Scan
Please run RogueKiller once again, and this time press: Scan
 When done, please post its new RKreport (Mode: Scan).
When done, please post its new RKreport (Mode: Scan).
However, after you post these results, do the following:
 Once again, please run Malwarebytes Anti-Malware
Once again, please run Malwarebytes Anti-Malware
Right-click the program and select: Run as Administrator
If an update is found, the program automatically updates itself.
At the program console, on the Scanner tab, and select: Perform Quick Scan
Next, click on the Scan button.
When the Malwarebytes scan is completed, click on: Show Results
When presented with a screen showing the malware detected, make sure everything is Checked, and click on:
Remove Selected
When removal is completed, a report opens in Notepad.
 Please copy/paste the entire contents of the MBAM report in your reply.
Please copy/paste the entire contents of the MBAM report in your reply.
 Restart the computer if MBAM did not request for you to do so!
Restart the computer if MBAM did not request for you to do so!
 Download: Malwarebytes : Malwarebytes Anti-Rootkit
Download: Malwarebytes : Malwarebytes Anti-Rootkit
Save to the Desktop
Right-click the file and select: Extract here...
Follow the Usage instructions, but, please stop at Step 5:
Usage
1.Download Malwarebytes Anti-Rootkit from the link to the right.
2.Run the file and follow the onscreen instructions to extract it to a location of your choosing (your desktop by default).
3.Malwarebytes Anti-Rootkit will then open, follow the instructions in the wizard to update and allow the program to scan your computer for threats.
4.Click on the Cleanup button to remove any threats and reboot if prompted to do so.
5.Wait while the system shuts down and the cleanup process is performed.
When the program is done, two reports are created in the mbar folder:
1. system-log.txt
2. mbar-log-2013-08-26 (20-13-32).txt (corresponds to mbar-log-year-month-day (hour-minute-second).txt)
 Please provide the mbar-log and the system-log.txt in your reply.
Please provide the mbar-log and the system-log.txt in your reply.
-
New #73
Okay, here is RKiller's new scan report:
RKreport[0]_S_08272013_102605.txt
Now moving on to MBAM Anti-Malware and Anti-Rootkit
@jumanji, no dice with the SD card I went ahead and formatted it.
I went ahead and formatted it.
-
New #74
... and the report from MBAM anti-malware
mbam-log-2013-08-27 (10-34-12).txt
and anti-rootkit...
mbar-log-2013-08-27 (11-02-45).txt
system-log.txt
How am I looking now?
-
New #75
That was expected, unfortunately. I have no idea what all that malware does.
Still there is one last-ditch attempt to try and recover any data if possible.( If the files had been overwritten by the malware you will of course draw a blank. Inevitable.)
Prepare a MSDOS bootable pen drive again with Rufus. (Select MSDOS in the dropdown box instead of ISO and then click on Start)
Download the Dos/Win9x version of Test Disk from TestDisk Download - CGSecurity
Extract the Zip file.
It will be extracted into a folder named testdisk-6.14. Select all the files in that folder and copy those to the DOS bootable pen drive you had created. Boot from the pen drive with the SD Card plugged in. Against the command prompt type photorec.exe and press enter to run it. On how-to Guide to using PhotoRec recovery software.
If it can dig out your files, you can copy them to your internal drive.
Anyway, try this only after you get an all-clear from cottonball. Most probably he is sleeping now.:)
From what I have seen, I see some DNS registry entries in the RK Report. The whois reports this:
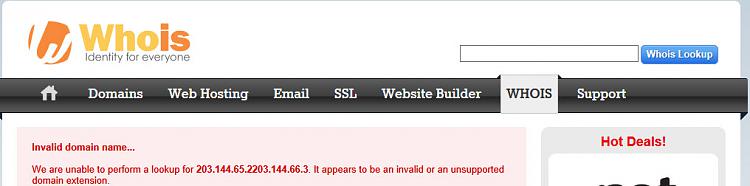
Do these point to the malware server msqjiol.com and should these be deleted? I would think so.
Let cottonball and other experts give their take on it.Last edited by jumanji; 27 Aug 2013 at 04:00. Reason: Minor additions/corrections
-
New #76
ducat1base,
Good job!!
On the following:
¤¤¤ Registry Entries : 2 ¤¤¤
[DNS] HKLM\[...]\CCSet\[...]\{FD384747-C343-4AE3-B338-90B3725EC0E4} : NameServer (203.144.65.2 203.144.66.3) -> FOUND
[DNS] HKLM\[...]\CS001\[...]\{FD384747-C343-4AE3-B338-90B3725EC0E4} : NameServer (203.144.65.2 203.144.66.3) -> FOUND
Registry key for CS001:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{FD384747-C343-4AE3-B338-90B3725EC0E4}]
Geo information on: (203.144.66.2 203.144.66.3)
Location Phnom Penh, Phnum Penh, Cambodia (KH)
Cambodian ISP, Country Wide, Wireless IAP
Is this familiar to you?
The Scan reports any DNS configurations found.
However, it does not mean the entries are malware related.
If I recall correctly, this laptop has a unique connection.
Try entering the following in WhoIs: http://whois.net/ip-address-lookup/
203.144.66.2
or...
203.144.66.3
What is queried now is: 203.144.66.2203.144.66.3
MBAM and MBAR report no malware.
Question for you...
Are there any other USB pen drives, SD cards, or removable media in your possesion that are more than likely infected?Last edited by cottonball; 27 Aug 2013 at 10:36.
-
New #77
Good analysis setting at rest that those can be malware related.
So it is his ISP related and he may sleep in peace.:)
(oh! I have been so stingy! have to spread before I rep.)
A job well done cottonball.
-
New #78
Thanks, jumanji!
A job well done to you also. You provided ducat1base with info for future use.
You provided ducat1base with info for future use.
Also, there may be other SD cards or USB data devices that need attention.
It's not over until it's over!!
 While we are at it, lets check your Security status with the following...
While we are at it, lets check your Security status with the following...
Download Security Check:
http://screen317.spywareinfoforum.org/
Save to your Desktop.
Double-click: SecurityCheck.exe
Follow the onscreen instructions inside the black box.
When done, a Notepad report opens automatically, called: checkup.txt
 Please post the checkup.txt in your reply.
Please post the checkup.txt in your reply.
(Please do not take any corrective actions!)
-
New #79
That DNS, I'm assuming, would be my VPN carrier. Are we starting to see the light at the end of the tunnel?
Here's the Security Check report:
checkup.txt
Yes, I believe I do have an external and another SD card which are infected.
-
New #80
Are we starting to see the light at the end of the tunnel?
Yes! You done gooood!!
Let's take care of some details, you do not need any vulnerabilities...
 Java version out of Date!
Java version out of Date!
Please update your version of Java:
java.com: Java + You
Also, uninstall all older versions of Java from your system.
They present a serious security risk.
Why should I uninstall older versions of Java from my system?
 Adobe Reader out of Date!
Adobe Reader out of Date!
Adobe Reader, latest version:
Adobe - Adobe Reader download - All versions
(Uncheck the following: Yes, install McAfee Security Scan Plus)
When done, go to Start > Control Panel > Programs and Features > Uninstall List
Look for, and remove any older Adobe Reader versions.
 Now, on the other SD card, and the external drive...
Now, on the other SD card, and the external drive...
Do not plug them in yet.
Do you remember if there are images on these that have also 'disappeared'?
Related Discussions


 Quote
Quote