How to Open and Use Event Viewer in Windows 7
InformationEvent Viewer is a tool that displays detailed information about significant events on your computer. Event Viewer can be helpful when troubleshooting problems and errors with Windows and other programs.
This tutorial will show you the basics about how to open and use Event Viewer to read the information in event logs in Windows 7.
NoteEvent logs are special files that record significant events on your computer, such as when a user logs on to the computer or when a program encounters an error. Whenever these types of events occur, Windows records the event in an event log that you can read by using Event Viewer. Advanced users might find the details in event logs helpful when troubleshooting problems with Windows and other programs.
Event Viewer tracks information in several different logs.
Windows Logs:
The Windows Logs category includes the logs that were available on previous versions of Windows: the Application, Security, and System logs. It also includes two new logs: the Setup log and the Forwarded Events log. Windows logs are intended to store events from legacy applications and events that apply to the entire system.
Applications and Services Logs:
- Application (program) - Events are classified as error, warning, or information, depending on the severity of the event. An error is a significant problem, such as loss of data. A warning is an event that isn't necessarily significant, but might indicate a possible future problem. An information event describes the successful operation of a program, driver, or service.
- Security - These events are called audits and are described as successful or failed depending on the event, such as whether a user trying to log on to Windows was successful.
- Setup - Computers that are configured as domain controllers will have additional logs displayed here.
- System - System events are logged by Windows and Windows system services, and are classified as error, warning, or information.
- Forwarded Events - These events are forwarded to this log by other computers.
Applications and Services Logs vary. They include separate logs about the programs that run on your computer, as well as more detailed logs that pertain to specific Windows services. This category of logs includes four subtypes: Admin, Operational, Analytic, and Debug logs.
For the source and more information about Event Viewer, see also:
- Admin - These events are primarily targeted at end users, administrators, and support personnel. The events that are found in the Admin channels indicate a problem and a well-defined solution that an administrator can act on. An example of an admin event is an event that occurs when an application fails to connect to a printer. These events are either well documented or have a message associated with them that gives the reader direct instructions of what must be done to rectify the problem.
- Operational - Operational events are used for analyzing and diagnosing a problem or occurrence. They can be used to trigger tools or tasks based on the problem or occurrence. An example of an operational event is an event that occurs when a printer is added or removed from a system.
- Analytic - Analytic events are published in high volume. They describe program operation and indicate problems that cannot be handled by user intervention.
- Debug - Debug events are used by developers troubleshooting issues with their programs.
WarningIf you are not logged on as an administrator, you will only be able to change settings that apply to your user account, and some event logs might not be accessible.
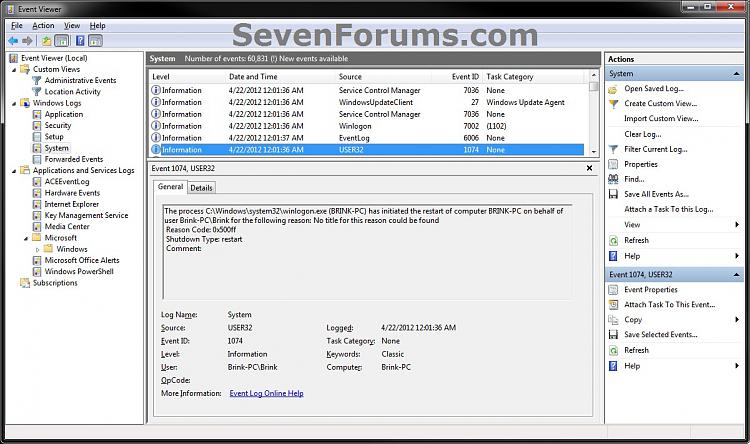
EXAMPLE: Event Viewer
Here's How:
1. Open the Start Menu, type eventvwr.msc, and press Enter.
2. If you are logged in as an administrator and prompted by UAC, then click on Yes.
3. In the left pane, click on an event log to see it's events listed at the top of the middle pane.
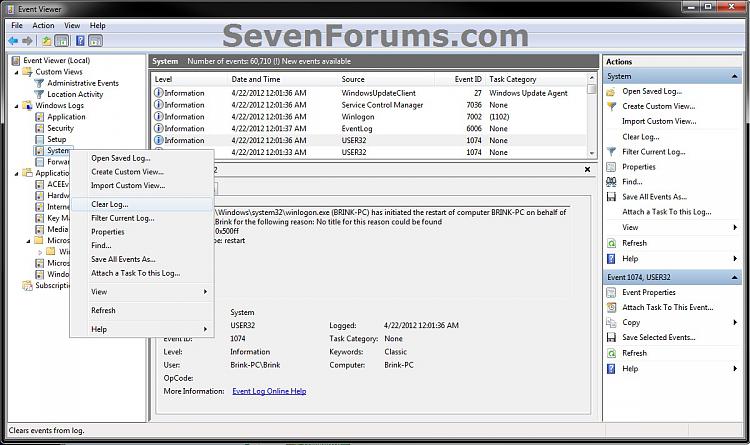
4. If you like, you could also right click on an event log in the left pane for more options to use. For example, to Filter Current Log or Find a specific event ID number listed in the middle pane.
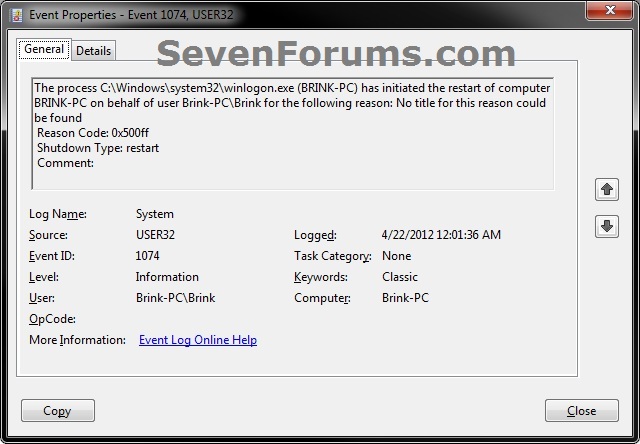
5. At the top of the middle pane, click or double click on a listed event to view the details of the event.
NoteEvent Properties
Event properties that can be displayed by adding columns to the Event Viewer display. In Event Viewer, you can click on View (menu bar) and Add/Remove Columns to do so.
- Source - The software that logged the event, which can be either a program name, such as "SQL Server", or a component of the system or of a large program, such as a driver name. For example, "Elnkii" indicates an EtherLink II driver.
- Event ID - A number identifying the particular event type. The first line of the description usually contains the name of the event type. For example, 6005 is the ID of the event that occurs when the Event Log service is started. The first line of the description of such an event is "The Event log service was started." The Event ID and the Source can be used by product support representatives to troubleshoot system problems.
- Level - A classification of the event severity. In the Event Viewer normal list view, these are represented by a symbol.
- Information - Indicates that a change in an application or component has occurred, such as an operation has successfully completed, a resource has been created, or a service started. Can occur in the system and application logs.
- Warning - Indicates that an issue has occurred that can impact service or result in a more serious problem if action is not taken. Can occur in the system and application logs.
- Error - Indicates that a problem has occurred, which might impact functionality that is external to the application or component that triggered the event. Can occur in the system and application logs.
- Critical - Indicates that a failure has occurred from which the application or component that triggered the event cannot automatically recover. Can occur in the system and application logs.
- Success Audit - Indicates that the exercise of a user right has succeeded. Can occur in the security log.
- Failure Audit - Indicates that the exercise of a user right has failed. Can occur in the security log.
- User - The name of the user on whose behalf the event occurred. This name is the client ID if the event was actually caused by a server process or the primary ID if impersonation is not taking place. Where applicable, a security log entry contains both the primary and impersonation IDs. Impersonation occurs when the server allows one process to take on the security attributes of another.
- Operational Code - Contains a numeric value that identifies the activity or a point within an activity that the application was performing when it raised the event. For example, initialization or closing.
- Log - The name of the log where the event was recorded.
- Task Category - Used to represent a subcomponent or activity of the event publisher.
- Keywords - A set of categories or tags that can be used to filter or search for events. Examples include "Network", "Security", or "Resource not found."
- Computer - The name of the computer on which the event occurred. The computer name is typically the name of the local computer, but it might be the name of a computer that forwarded the event or it might be the name of the local computer before its name was changed.
- Date and Time - The date and time that the event was logged.
- Process ID - The identification number for the process that generated the event.
- Thread ID - The identification number for the thread that generated the event.
- Processor ID - The identification number for the processor that processed the event.
- Session ID - The identification number for the terminal server session in which the event occurred.
- Kernel Time - The elapsed execution time for kernel-mode instructions, in CPU time units.
- User Time - The elapsed execution time for user-mode instructions, in CPU time units.
- Processor Time - The elapsed execution time for user-mode instructions, in CPU ticks.
- Correlation Id - Identifies the activity in the process for which the event is involved. This identifier is used to specify simple relationships between events.
- Relative Correlation Id - Identifies a related activity in a process for which the event is involved.
That's it,
Shawn
Related Tutorials
- Filtering and Creating Custom Event Views for System Monitoring
- How to Setup Event Viewer in Vista and Windows 7 to Send a Email Notification
- How to Monitor Boot Times in Event Viewer
- How to Clear the Windows 7 Event Viewer with One Click
- How to Read the Event Viewer Log for Check Disk (chkdsk) in Windows 7 and Vista
- How to Read the Event Viewer Log for Memory Diagnostics Tool
- How to Read the Wake Source Log in Event Viewer for Windows 7 and Vista
- How to See the Last Shutdown and Restart Time of Your Windows PC
Event Viewer - Open and Use in Windows 7
-
-
-
New #3
Wow! Very nice work Brink! Serious dedication there.
-

Event Viewer - Open and Use in Windows 7
How to Open and Use Event Viewer in Windows 7Published by Brink
Related Discussions




 Quote
Quote